Azqa Nadeem
Faculty of Electrical Engineering, Mathematics & Computer Science
Clustering Malware's Network Behavior using Simple Sequential Features
Azqa Nadeem was first introduced to the world of cybersecurity during a Bachelor’s internship. It was a subject where she could combine her experience in computer technologies with her interest in finding what makes devious people tick. She realized that antiviruses were not as good at protecting computers from cybercriminals as she had thought. She also found that the lack of transparency in detection methods makes it more difficult to build systems that consistently improve security. The choice of her thesis topic was rooted in the idea that better security can be achieved by making it easier for the defenders to understand attacks.
Working on her MSc thesis made her realize how fundamentally difficult it is to understand a piece of malicious software, and that a mere nine month project would only just scratch the surface. She now works as a PhD researcher and junior lecturer at the Cyber Security Group. In both her MSc and PhD projects, she aims to uncover hidden relationships between different pieces of malicious software, and then use these relationships to predict the future of malware and understand how to detect it before it even exists.
I am confident that her passion and commitment towards her work, and her resolute work ethic, will propel her towards a successful career.
Graduation committee - Dr.ir. S.E. Verwer, prof.dr. P.H. Hartel, dr.ir. C. Hernandez Ganan, dr. Z. Al-Ars
In this digital age, attackers use malicious software – malware – to steal sensitive information like healthcare or banking details. Millions of malware files are detected every day. Based on their similarities, they are categorized into families to make it easier to identify them. However, this categorization uses Machine Learning (ML) that often leads to classification mistakes. It also applies multiple filtering and averaging steps, which turns this analysis into a "black box", giving little control to human investigators.
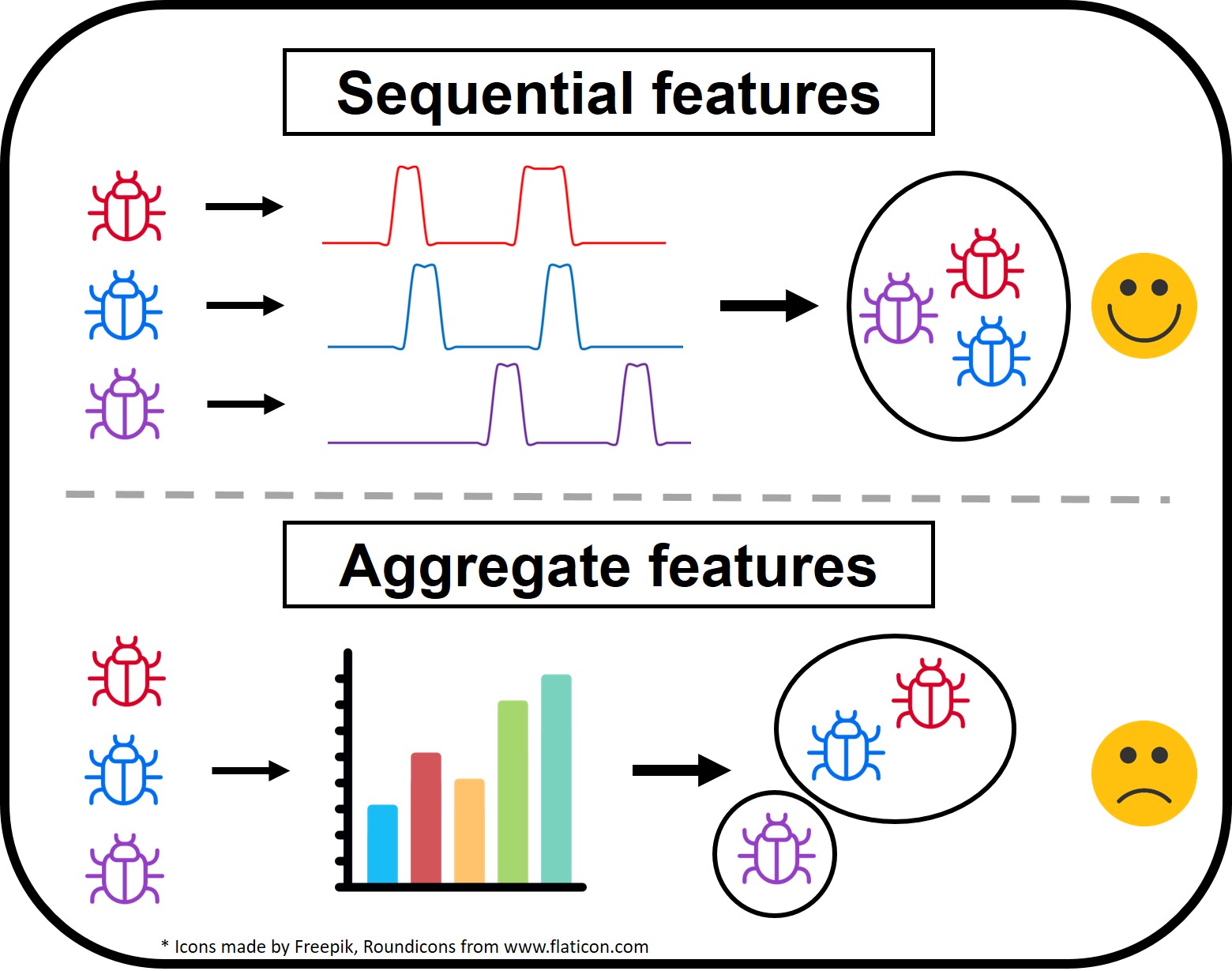
In her thesis, Azqa explores the possibility to use malware’s “sequence of actions” to build a simplified analysis pipeline, and use that to identify malware’s attacking behaviours. She also introduced a visualization technique to assist investigators in better understanding malware. The method she proposed uncovers interesting behaviours like multiple malware families being controlled by the same attacker, and device scanning behaviour before an attack happens. This method creates fundamental improvements in threat analysis that will improve computer security for all.