There is no such thing as an un-hackable power grid, one can only try to make it as hard as possible for the adversaries.
Charging your phone at night before you go to sleep, keeping your laptop powered during lectures and monitoring the heartbeat of a patient in a hospital. All these processes are taken for granted in first-world countries, but all rely on functioning electricity grids. When the power supply is interrupted in a country due to a cyber-attack on the grid, society in that country seizes to function as is. Because access to power is so critical, it should be highly protected. For this reason Quincy Abel, Master student Complex Systems Engineering and Management (CoSEM), decided to look at the state of protection of power grids against cyber-attacks from malicious actors (read: hackers), and how to better protect them with well-made cybersecurity investments.
How did this research about the protection of power grids come to you?
I first heard about the Control Room of The Future, while following the online DelftX course “Digitalization of Intelligent and Integrated Energy Systems”. In this course, among other things, the cybersecurity of the power grid was discussed. Here I first heard how the modern power grid was protected against malicious actors and how this protection was lacking in many cases due to legacy infrastructure and outdated protocols. This specific part of the lecture was given by Assistant Professor Alex Stefanov. I finished the course and learned many things, but did not focus on this subject anymore. This all changed when I was following the course Cyber Risk Management by Professor van Gelder and we were treated to a guest lecture presented by no one other than Alex Stefanov. This guest lecture was about the topic of cyber security of power grids. At the end of the guest lecture it was mentioned that they were looking for multidisciplinary students to write a master thesis about this subject, and from that moment on I was sold. So I contacted the professors the next day, and the rest is history.
What was your research question and how did you answer it?
My research question was: “To what extent can cyber security measures decrease the risk of cyber-attacks on CPPS substations?” and it has been answered by two literature reviews, modelling the digital substation layout and running and analysing certain cyberattack-defence scenarios.
Can you tell us more about the research you conducted?
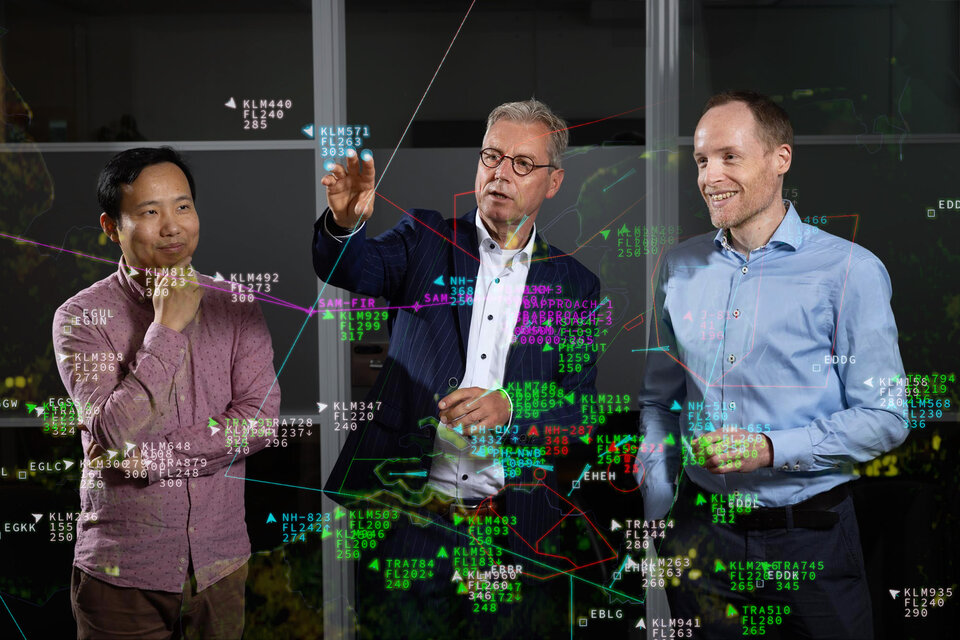
In order to answer my main research question I would have had to model the (digital) infrastructure of a modern substation, determine how hackers could infiltrate this substation and how long it would take them to reach their end goal. Luckily I worked closely with Ioannis Semertzis, who is a PhD candidate at the Control Room of The Future. He previously modelled a similar system and was extremely helpful during my thesis period. In the Control Room of The Future, a high-end simulation control room at the EWI building, many researchers dedicated their time and effort to simulate, among others, the European grid and its behaviour under different circumstances. The knowledge that is gained in that room is very useful for real life protection of the power grid. For example: One of the simulations that they have shown is the Rolling Blackout scenario. In this scenario you can see (on all the many screens in the room) how an entire section of the power grid can be taken down if just a handful of specific substations are attacked simultaneously. This was very impressive to witness as the room is built to look very similar to the control room of one of the big Transmission System Operators in Europe.
What was your main focus in this project and how did you researched this?
The main focus of my project was to see how (digital) substations could be better protected against malicious actors, while taking into account the budgetary constraints of Distribution System Operator organizations.
I researched what type of protection (e.g. firewall, two-factor authentication, etc) would offer the best protection against cyber-attacks, and where these counter measures should be placed. The placement of the counter measures was a big part of the research, because there are a lot of ways/methods (read: exploits) that can be used by a malicious actor to reach its end-goal. Let’s take a simple security example: imagine that you want to protect a house against burglary. You could buy an expensive titanium reinforced door with eye-scanning technology to keep the burglars out. But, this counter measure would be useless to deter burglars if there is a window open right next to the door. In that case you have wasted money on a flashy counter measure but its effect is diminished due to the alternative offered to the burglar. This is basically what I was modelling and researching during my master thesis.
Did you recognize topics from your Master course during the fieldwork project?
Absolutely, I recognized a great deal of topics from my Master CoSEM during the thesis project. I will just focus on the two most prominent topics I recognized. The first topic was System-of-Systems. This basically comes down to the fact that systems (in my case, substations) are not operating in isolation but are often part of a much larger system (which in my case was the broader power grid). When dealing with System-of-Systems was important to regularly zoom in and out to maintain the right level of abstraction to deal with the challenges at hand. This System-of-Systems thinking is one of the overarching themes that CoSEM addresses. The second topic was networks. This one is quite self-explanatory; the power grid is basically a large network of copper cables through which the current flows, and the (digital) substations are part of the communication network that controls the behaviour of the power grid. And within the substations you have a network of routes that a malicious actor can take to shut down or disturb the substation. The last network, the network within the substation, is what I focused on. I used algorithms that I had learned during the Design in Networked Systems course, to build a model that could calculate how fast an entire substation could be compromised. And it was faster than expected.
What were you most looking forward to beforehand?
I looked forward to working with the talented people of The Control Room of The Future, and to apply all the knowledge of my studies to this cybersecurity challenge.
What is the most important thing you have learned?
I have learned that you should never be afraid to jump out of your comfort zone and face a challenge that seems almost impossible for you to overcome. Because, with the right guidance, endurance and patience, you can do many times more than what you thought you were capable of. My biggest challenge was actually coding my model, as I have not really used Python that much before starting my thesis. But, when my model was finally giving me results that I could work with after weeks of coding I was super happy.
How will the project proceed?
My thesis was just a small part of the broader research that is being done at the Control Room of The Future. The findings were used to answer my main research question. Some of the findings might be published in an article that I am writing for the International Journal of Security and Networks
What are your own plans?
Right now I am employed as a Business Engineer for Oxand in The Netherlands. I am working on a large infrastructure project on “de Zuidas” and also on a smaller risk management project for the Municipality of Amsterdam.